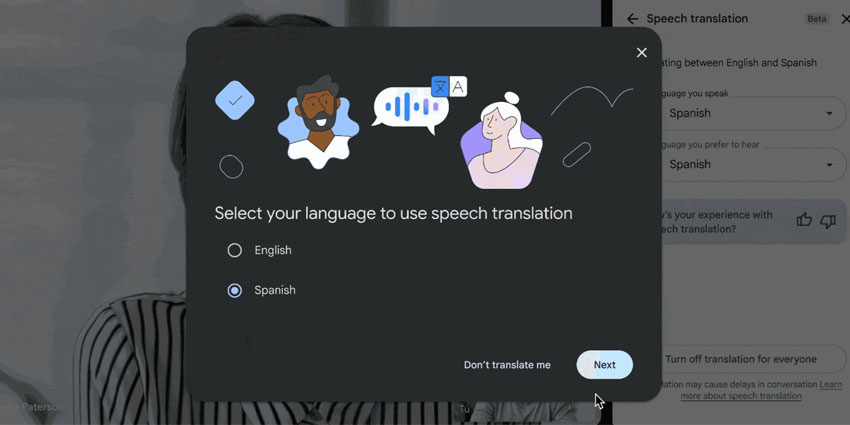
Cybercriminals are targeting Microsoft Teams users with “vishing” attacks.
As Trend Micro initially reported, bad actors are using social engineering techniques through Teams calls to impersonate user clients and gain remote access to their systems.
Vishing, short for “voice phishing,” is similar to phishing in that it involves attempting to trick someone into providing sensitive information or granting access to a system. However, unlike traditional phishing, vishing is conducted over the phone or through a calling app.
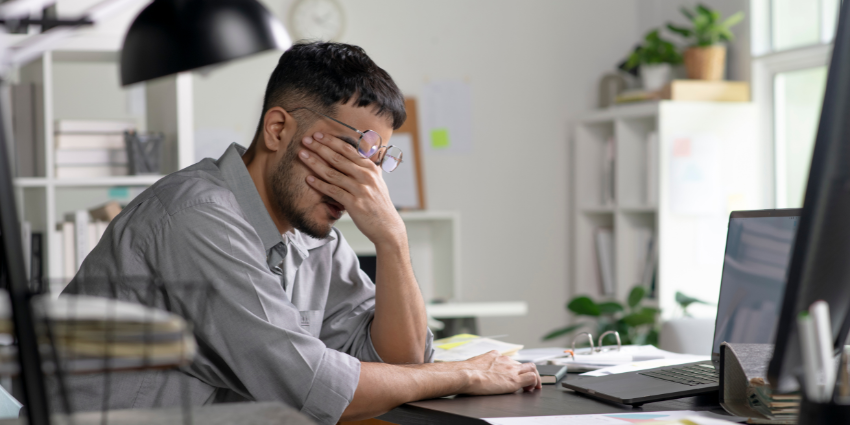
As Trend Micro outlines, the attack began with a flood of phishing emails overwhelming a victim’s account. The cybercriminal then followed up with a phone call, posing as a tech support assistant and offering to “resolve” the problem they had triggered. This tactic exploits the victim’s frustration and urgency to fix the problem, tricking them into granting access or sharing sensitive information.
Although the attacker, in this instance, failed to install a Microsoft Remote Support app, they successfully convinced the victim to download AnyDesk, a remote access tool.
Trend Micro’s team wrote:
Using Vision One, we observed a recent security incident in which a user was targeted by an attacker posing as an employee of a known client on a Microsoft Teams call. This led to the user being instructed to download the remote desktop application AnyDesk, which then facilitated the deployment of DarkGate malware.”
To deploy the DarkGate malware, which cybercriminals commonly use to steal data and gain control over a victim’s computer, the bad actor used the remote access app to install a PowerShell-based malware dropper on the victim’s system. This malware dropper then fetched the DarkGate malware.
DarkGate operates as a Remote Access Trojan (RAT), allowing the attacker to control the infected system remotely, steal sensitive information, and further compromise it.
The attack was stopped before anything was stolen, but the case illustrates the increasing (and alarming) sophistication of myriad cyberattack strategies and technologies.
A Challenging Cybersecurity Year For Microsoft
Microsoft has mobilised the equivalent of 34,000 full-time engineers for its Secure Future Initiative (SFI), a sweeping effort to enhance its security infrastructure following high-profile breaches.
The first SFI launched in November 2023 after a series of cybersecurity incidents, including the Storm-0558 attack in July 2023. This breach, attributed to Chinese hackers, compromised US government emails through vulnerabilities in Microsoft Exchange Online. In April 2024, the US Cyber Safety Review Board (CSRB) criticised Microsoft for inadequate preventative measures.
In response, Microsoft has fortified its SFI, pledging to adopt the CSRB’s recommendations. The company has also unveiled robust security principles and objectives, underscoring its commitment to strengthening cybersecurity across its platforms.
Moreover, in May, Microsoft announced it was linking the fulfilment of security goals with executive compensation in an expansion of SFI. That was further expanded upon in August when a leaked Microsoft memo outlined that not producing substantial work focused on security could negatively impact every worker’s salary increases, promotions, and bonuses. This further extension of that policy to every employee seemingly intends to underscore its commitment to “making security (its) top priority, above all else”.
Since the news of the large number of full-time SFI engineers broke, however, there have still been notable incidents, of which this vishing story is just one.
For instance, in October, it emerged that the ransomware group Black Basta has adopted a deceptive new tactic: impersonating Microsoft Teams IT support to breach enterprise systems and steal sensitive data. Their approach involves bombarding targeted employees with spam emails and then masquerading as the Microsoft helpdesk to offer assistance in resolving the issue.